Create
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Community resources
Community resources
Community resources
Integrate Jira/Confluence with Active directory
February 25, 2021 edited
Step By Step Explanation on How to Integrate JIRA/ Confluence with AD/LDAP
Points to be considered.
- Some Active Directory knowledge(pre-requisite)
- Users and groups container must be created in active directory for example (DEVGB -> user_a, user_b, user_c and so on)
- Create groups in active directory were users will belong to in order to be able to access jira/Confluence (for instance active_jira_users, active_confluence_users), application access must also be configured in your Jira/Confluence server using these groups
- In my case I use jira-internal directory to manage users in my confluence server
- Nested groups would be used in active directory( for instance, Jira user, confluence users group should be a member of for instance atlassian_users , so that you can iterate user search for more that one group.
- To use both Jira internal directory and Active directory you must change the order of directories, in case of active directory usage then it should be the first directory on the list.
- To make life easy for other external users you may want to create a possibility for user’s to be able to change their password, via outlook for example if your outlook uses active directory credentials
- Since you will be using Active directory user credentials then all user names in you Jira internal directory
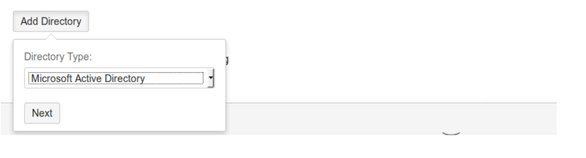
- Go to user management as Jira Administrator them choose user directories and then click on Add Directory , under Directory Type Choose Microsoft Active directory if you are using AD or LDAP which ever the case might be in my case i use active directory and then click Next
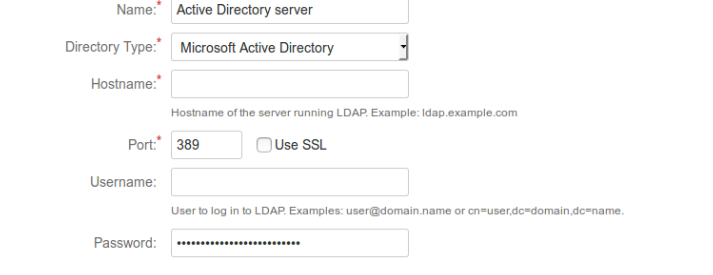
- You will be prompted to the next window which is the Configure LDAP User Directory window and then you have to fill in the required fields and other fields on the server settings
- Directory Type must be Microsoft Active Directory in this case, next is Hostname of the server running your Active directory enter your hostname for example ldap.example.com by default Port number is 389, if you have SSL(Secure socket layer configured to the server running your AD(Active directory or LDAP) then Check Use SSL, the default number will be changed to 636
- Next is the User name and Password you will need to have a user(special) that will access LDAP/AD for Example the syntax for Username is user@domain.name or cn=user,dc=domain,dc=name. Where cn means common name and dc means domain component. And then enter user’s password.
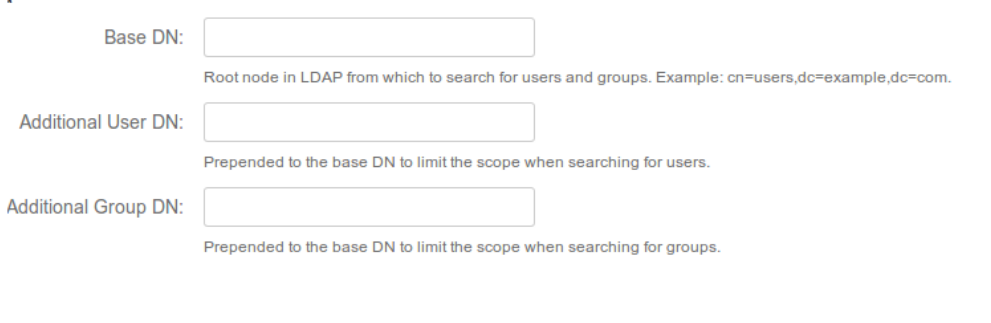
Hint: To use the second syntax for user name you need to log in to your AD/LDAP, find the user you would like to use to access AD/LDAP go to user Properties Attribute Editor and look for the attribute distinguishedName, there you will find the correct syntax for the user. - So far so good, Next in line is the LDAP/AD scheme which has the field Base DN (Base Distinguish Name) here you will need to fill in the rootnode in LDAP/AD from which to search for users and groups. How to get the base DN ? you will need to log in to your LDAP or AD and right click on the container where users and groups are keep inside for example container RD , once again go to Properties Attribute Editor a nd look forthe attribute distinguishedName, there you will find the correct syntax for the user for example OU=RD,DC=mega,DC=megaint,DC=com
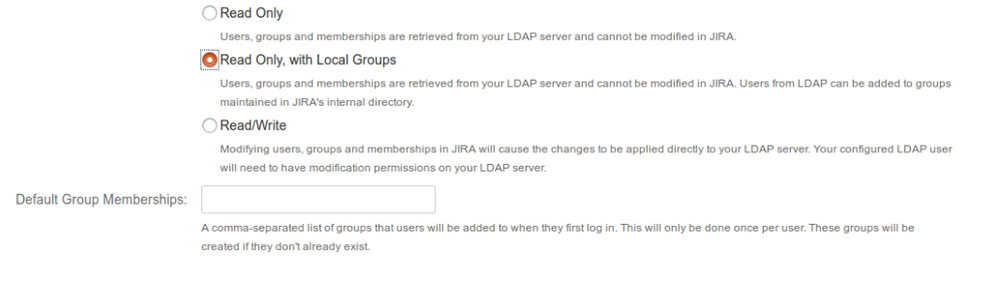
- Now you will have to set permission under LDAP permission scheme, here you should choose Read only,with Local Groups so that you can add groups from jira internal directory to LDAP users.
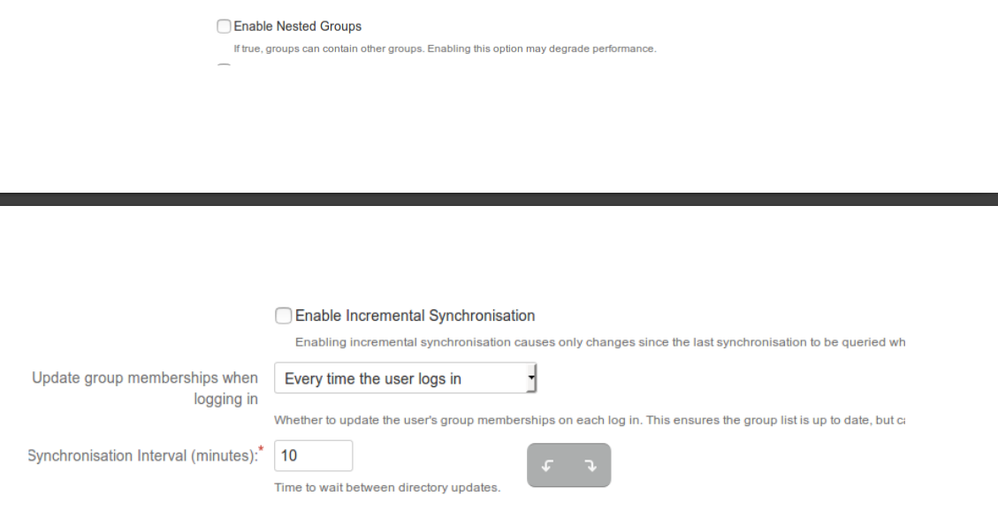
- Further more, we have the Advanced setting here you need to be a little bit careful with the fields you mark checked. make sure you don't enable Nested groups because in our case we shall be managing group from JIRA Internal directory not from LDAP/AD it self, and our JIRA instance is not configured to have nested groups and in fact when you have your JIRA instance configured to have nested groups and you are managing groups which are nested in JIRA internal directory this could affect logging in, permissions, and viewing and updating users and groups, thus degrading performance, Incremental Synchronization should also be unchecked, Update group memberships when logging in should be set to Every time user logs in and Synchronization interval should be set as you wish (5mins should be fine )
- Next thing to do is to configure the User Schema Settings all fields in this setting are automatically field in and the only field you need to modify is the User Object Filter
As I have mention earlier, in active directory in a container you have to create groups for example Active_Jira_users, Active_confluence_users, Active_EXT_jira_users which will give access to Jira/Confluence to users, group names must be the same (not case sensitive) in Jira internal directory
and configured in Jira application access configuration. these groups, must be a member of one group Atlassian_users for example so that we can recursively search for user in nested groups using the syntax below for example
(&(objectCategory=Person)(sAMAccountName=*)(memberOf:1.2.840.113556.1.4.1941 :=CN=Atlassian_Users,OU=Groups-SD,OU=Groups,OU=PL,OU=RD,DC=mega,DC=mega,DC=com)) - More also, we have the Group Schema Settings, the only field you should modify is the Group Object Filter field all other mandatory fields
are field in by defaultFor example group object filter field can have the sample filter
(&(objectCategory=Person)(sAMAccountName=*)(member:1.2.840.113556.1.4.1941 :=CN=Atlassian_Users,OU=Groups-SD,OU=Groups,OU=PL,OU=RD,DC=mega,DC=mega,DC=com))
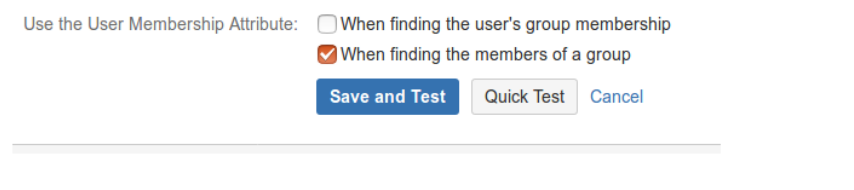
in this case also we are recursively iterating groups which belong to the parent group. - The final thing to do is to configure the Membership Schema Settings you will only need to check When finding the members of a group under the Use the User Membership Attribute field all other field are filled in by default and should not be modified.Then click save and test. Now you will have to try to login with an active directory user which you added to group Active_Jira_users, Active_confluence_users, which is responsible for user access.
Congrats your are good to go!!!!
Was this helpful?
Thanks!
Moses Thomas
Community Champion
About this author
Founder - Red Moth Technologies
Red Moth Tech / ATOS
Poland
156 accepted answers
Community showcase
Atlassian Community Events
Copyright © 2026 Atlassian
2 comments