Community resources
Community resources
Community resources
Biggest Data Breaches in healthcare in 2022 | How to avoid joining the Wall of Shame!
Regardless of how the healthcare data breach is caused, once more than 500 individuals are affected, your organization is placed in the public pillory, the HIPAA Wall of Shame. Public loss of trust joins the already horrendous penalties in the healthcare industry.
Find out, in this article, what the most serious data breaches were in 2022 and how you can confidently continue to use your software without getting an entry on the Wall of Shame!
What is the Wall of Shame?
The protection of protected health information (PHI) is regulated by the U.S. federal law HIPAA (Health Insurance Portability and Accountability Act). Once your company processes health information of U.S. citizens, and you are a health care provider, clearinghouse or health plan organization, you must comply with HIPAA guidelines.
Violations of HIPAA’s strict regulations can result in fines of up to $1.5 million per year, or even jail time. Under HIPAA’s HITECH Act, the U.S. Department of Health and Human Services (HHS) must publish a list of data breaches once 500 or more individuals are affected. Officially, the name of this HIPAA breach list is Breach Notification Portal. However, with a twinkle in the eye, it is referred to as the HIPAA Wall of Shame.
The HIPAA Wall of Shame entry of your company or institution remains public for the next 24 months. Older violations, however, are still accessible through the archives. This can cause your customers to lose confidence in your services. In addition, your healthcare institution may be subject to OCR oversight for one to three years.
Why is there a Wall of Shame?
The primary goal of the breach list is not to “shame” data violators, but to provide researchers with information on how to combat data breaches in the sensitive healthcare industry. After all, the better the research, the easier it is to analyze errors and prevent them in the future.
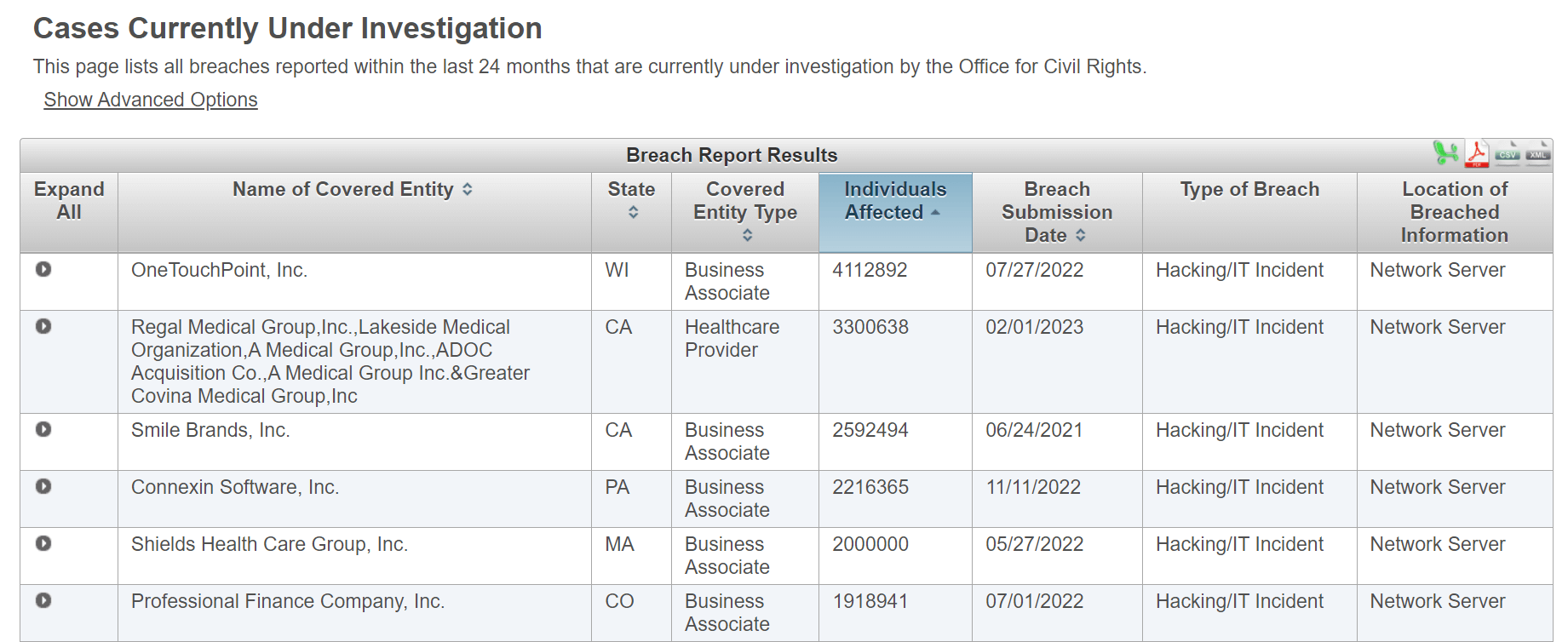
We don’t need to provide you with a mere listing of HIPAA breaches. You can find them directly on the Wall of Shame:
We, instead, want to work with you to analyze the healthcare data breaches of 2022 and find solutions for how you can avoid ending up on the Wall of Shame as well.
HIPAA violations in 2022
In 2022, 600 healthcare data breaches were reported by the HHS Office of Civil Rights. Among the most common HIPAA breaches were:
-
Hacking and viruses
-
Stolen electronic devices
-
Insecure digital or paper records
A breach of the Health Insurance Portability and Accountability Act (HIPAA) is more than expensive. Often, there is also the added concern of patient safety. After all, cyberattacks typically cause IT systems to fail. It’s unthinkable to run a medical practice or clinic if diagnostic and treatment data are unavailable.
Therefore, the following list is intended to guide us in making the critical healthcare systems more secure.
OneTouchPoint: 4.1 million affected patients
OneTouchPoint is a Wisconsin-based company that provides mailing, marketing and other services to healthcare organizations. In April 2022, unauthorized file access occurred to certain servers. Sensitive protected health information (PHI) such as names, patient records, ID numbers, patient demographics or service descriptions were exposed.
Many of the 35 healthcare organizations that use OneTouchPoint blame the company for reporting the security breach too late.
Lessons learned from this breach
-
Review your security measures regularly
-
Make sure your programs are HIPAA-compliant
-
Report HIPAA violations in a timely manner (within 60 days)
Advocate Aurora Health: 3 million affected patients
Advocate Aurora Health is one of Chicago’s largest healthcare providers, which runs 27 hospitals. In this HIPAA breach, certain internet tracking technologies from Google and Facebook led to the leak of some protected health information (PHI). These snippets of code, called pixels, were used to track interactions on patient portals. To prevent further harm, they have now been removed or disabled.
Lessons learned from this breach
-
For healthcare: provide HIPAA-compliant communications to your patients
-
For patients: Use browser tracker blocking features or incognito mode when logging into medical portals
Shields Healthcare Group: 2 million affected patients
Shields Healtcare Group was the victim of a cyberattack from March 7 to March 21, 2022. This company is a third-party vendor that provides MRI and ambulatory surgical services. The sensitive health data of more than 2 million patients was compromised during this period. However, the HIPAA violation was not discovered until March 28. Patient IDs, treatment information, insurance details and other data were stolen.
Lessons learned from this breach
-
Take a zero-trust approach to potential cyber threats
-
Consider the 60-day breach notification period
Broward Health: 1.35 million patients affected
In January 2022, Broward Health suffered data theft of 1.34 million patients and employees through the hack of a connected third-party vendor. In this case, affected individuals were also notified after the 60-day deadline. Social Security numbers, insurance information, account numbers and medical information were exposed. The cause of the HIPAA violation was believed to be a lack of multi-factor authentication, which allowed an unauthorized party to gain access to the Broward Health network through a third-party vendor’s office.
Lessons learned from this breach
-
Implement multi-factor authentications (MFA).
-
Monitor which users can access confidential resources
Prevent healthcare data breaches
Following the exemplary HIPAA breaches from 2022, it is now clear that every healthcare organization must take security measures to protect sensitive health information (PHI).
Here’s how to avoid HIPAA violations
-
Raise awareness and educate your employees
-
Nearly half of all privacy breaches can be traced back to phishing emails. Train your employees on what legitimate emails look like so no one from your organization clicks on a harmful link that may contain malware.
-
-
Minimize the risk of human error
-
Unauthorized individuals should not have access to critical health data. Permission schemes for your software can restrict viewing and editing of data for specific roles, thus securing it.
-
Also consider the case of Broward Health: a person walks into an office and gains on-site access to the server. Therefore, pay scrupulous attention to physical access to sensitive data as well.
-
-
Set up two-factor authentication (2FA)
-
If you have activated two-factor authentication for logging in, life is made difficult for hackers. The increased level of security for customer data is quick and easy to set up. Atlassian, for example, offers a guide for its customers on how to set up 2FA.
-
-
Avoid the Wall of Shame with the right tools
-
To manage health data, tasks and projects, and provide patients with a login portal, there are several software providers. Choose wisely and opt for systems, such as Jira and Confluence, that are fully HIPAA-compliant.
-
Conclusion: How to avoid the Wall of Shame
Healthcare organizations are inundated with immense amounts of sensitive data every day. To remain HIPAA-compliant despite the volume of data, you should first ensure that all employees understand the importance of data protection. This is where training and consulting can be beneficial.
Using healthcare project management applications that ensure HIPAA-compliant activities is essential in avoiding the Wall of Shame. Many hospitals and healthcare organizations already use Confluence and Jira software to manage patient data.
Was this helpful?
Thanks!
Andreas Springer _Actonic_
About this author
Head of Marketing
Actonic GmbH
Germany
2 accepted answers
0 comments