Community resources
Community resources
Community resources
Checklist. Security requirements [use case]
Have you ever faced any difficulties while working with security requirements in Jira? It’s not always easy to be aware of all aspects of security. To simplify this process for your company, consider two aspects below:
- check whether the product you are working with meets the requirements
- regularly track it with your team.
We at SaaSJet work with many security requirements and constraints from Atlassian. As a vendor, we must ensure that customers’ data isn’t stored, authorization is fully secured, data retention policies are met, etc. Here we want to share our experience of creating security checklists in Jira.
Types of security requirements
There are a lot of tasks you should take care of in order to build good security. Understanding the types of such duties increases your chances of avoiding security problems. Requirements may cover such items:
- Passwords and access control
- Audit logging and analysis
- Network and data security
- Role management and authorization
- Validation and code integrity testing
It would be handy to have a checklist for each. Let’s look at how you can do it.
How to organize security checklist in Jira
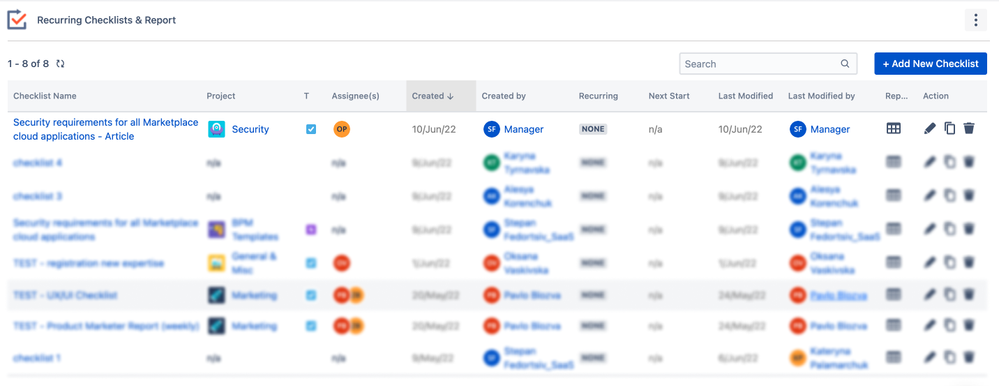
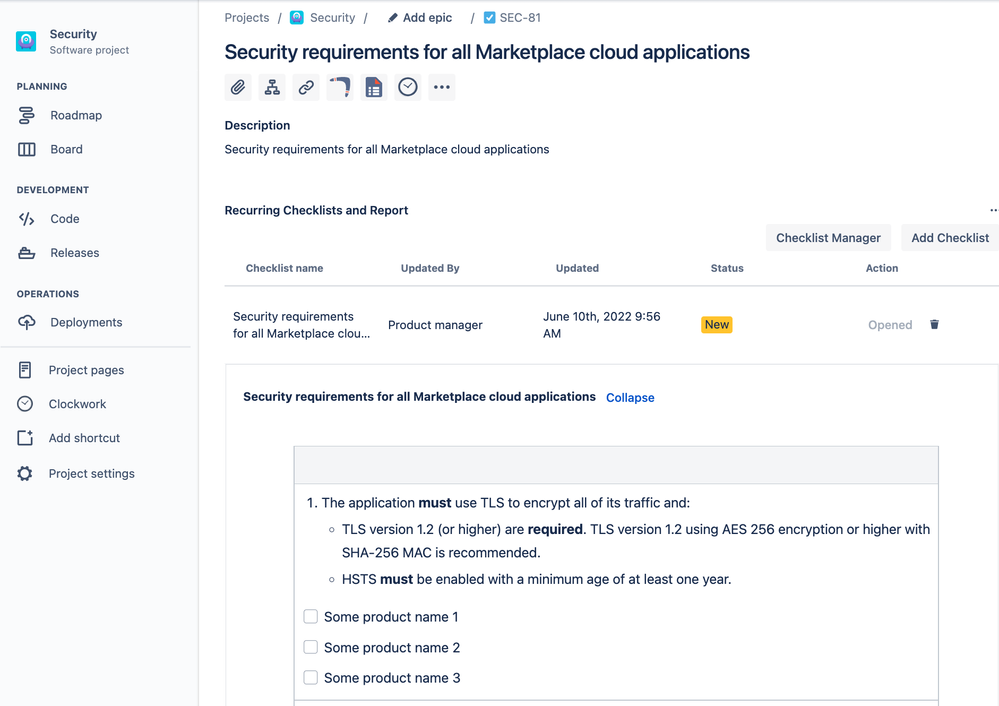
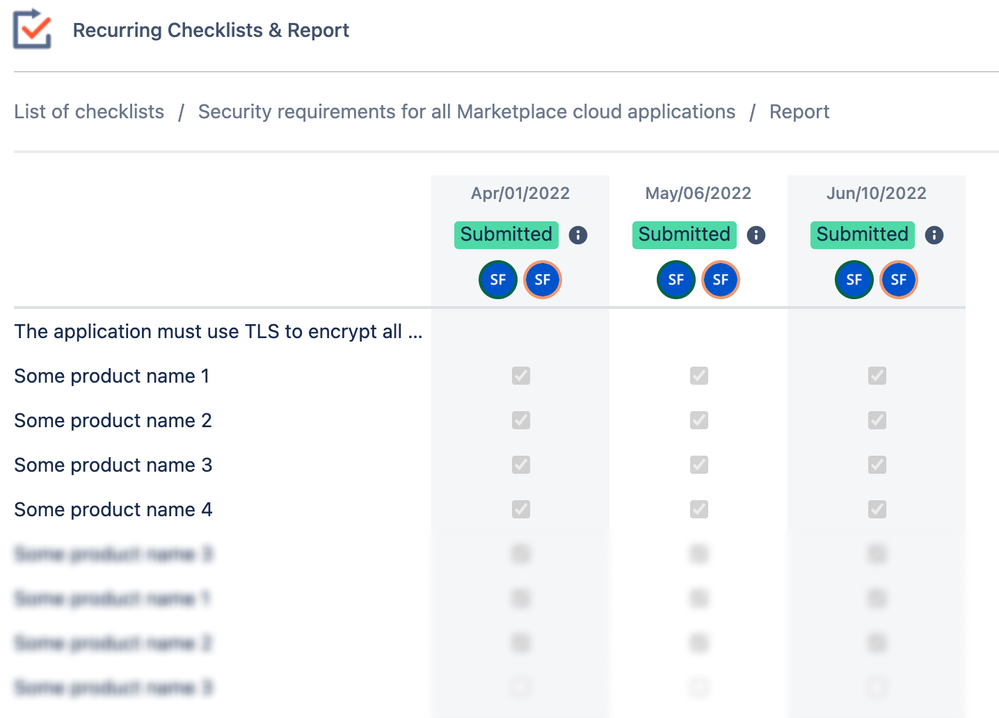
Security requirements are often well known. However, teams are constantly working on products, so new releases should follow the rules. Managers should always track security risks. That is why we create and use our tool – Recurring Checklists and Report for Jira. It allows the manager to create a checklist, assign it regularly to the responsible person, and get the result.
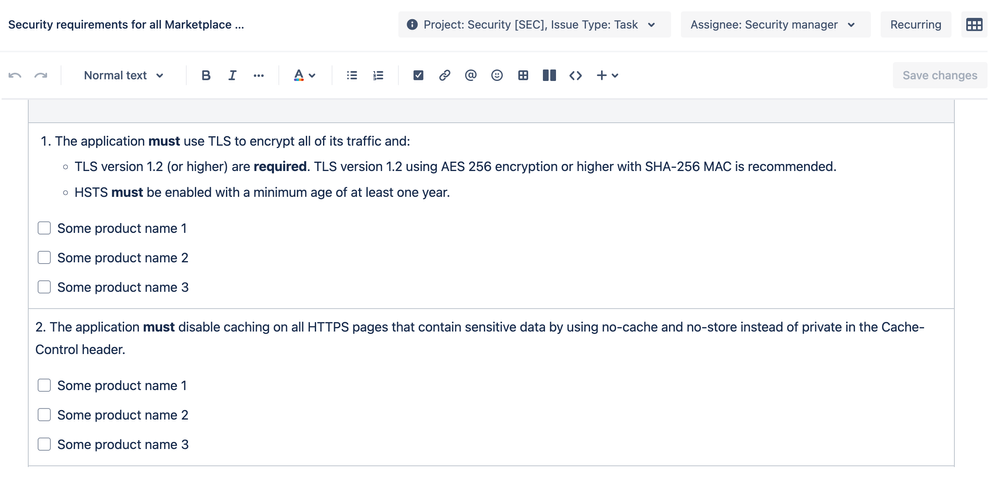
Inside the Checklist, we’ve entered the list of security requirements we should follow and the names of our add-ons.
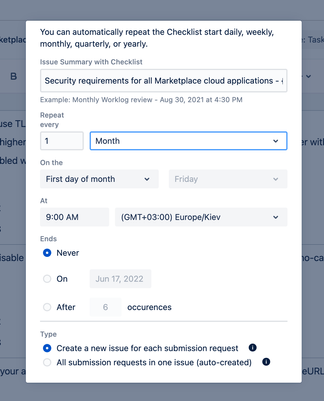
Also, we want this checklist to be completed every month for every product we actively work on. So, we set the recurrence that will automatically create the issue in the Security project and assign it to the manager. Then PM should give the resolution on whether we are fine against the requirement or not.
So, on the first Friday of every month security manager will receive the issue with the Checklist.
Once it’s completed, the manager can review the details on the issue-level or check the helicopter view report.
With this report, managers can monitor the progress over months and track if some items were selected as false.
Also, all new Checklist questions will be displayed in the report, so it is easy to track how checklists are changing over time.
Takeaway
Consider how are security requirements set in your company. Information security, privacy, and the protection of corporate assets and data are essential for every business. Try to create and track checklists to never miss critical steps of safety processes.
Was this helpful?
Thanks!
Karyna Tyrnavska _SaaSJet
About this author
Product Marketer
SaaSJet
14 accepted answers
TAGS
Atlassian Community Events
- FAQ
- Community Guidelines
- About
- Privacy policy
- Notice at Collection
- Terms of use
- © 2024 Atlassian





0 comments