Community resources
Community resources
SSL certificate is imported as a trustedCertEntry, tomcat is unable to start
Summary: I am trying to update the SSL certificate for our BitBucket server. I am seeing assistance installing the new ps7 certificate as a PrivateKey type on my keystore.
As per the instructions on confluence I created a local self-signed certificate on a new keystore titled "bitbucket-keystore", using the following command:
"%JAVA_HOME%\bin\keytool" -genkey -alias sc.phgic.com -keyalg RSA -sigalg SHA256withRSA -keystore <Bitbucket home>\shared\config\bitbucket-keystoreNext, I used the keytool to generate a CSR and submitted the CSR to our certificate authority (CA) for signing.
After receiving the download link from the CA, I downloaded the SSL certificate in PKCS7 format, and ran the following command to install it on my keystore:
"%JAVA_HOME%\bin\keytool" -import -alias sc.phgic.com -file sc_phgic_com.p7s -keystore <Bitbucket home>\shared\config\bitbucket-keystore
The import appeared to be successful. I restarted the BitBucket service, but it failed to start. I discovered the following exception in the logs: java.io.IOException: Alias name [sc.phgic.com] does not identify a key entry
I searched the Knowledge Base and found this related issue:
https://confluence.atlassian.com/bitbucketserverkb/unable-to-start-tomcat-due-to-java-io-ioexception-alias-name-not-identifying-a-key-entry-943541751.html
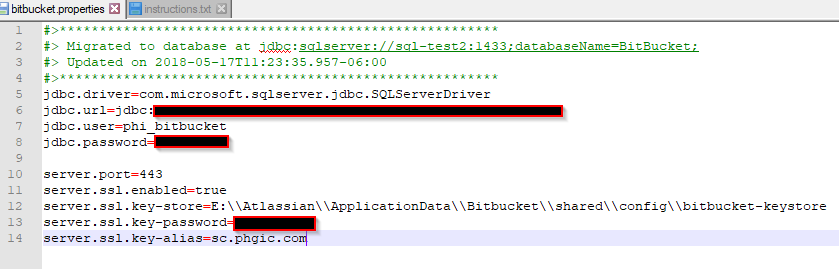
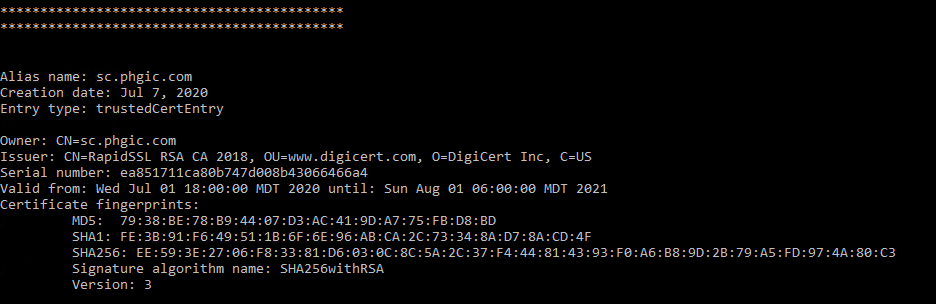
Re: Cause #1, I confirmed the alias in the keystore matches the alias in our configuration file, and the keystore does contain this alias:
So, I suspect the root problem is Cause #2 - entry type is trustedCertEntry instead of PrivateKey.
(I also tried installing the intermediate and server certificate as separate .cer files, and received the following error: Input not an X.509 certificate)
I would prefer to work with a single .p7s file; but, how can this be installed as a PrivateKey entry type rather than trustedCertEntry?
Is there possibly some other issue with the private key in my keystore preventing this certificate from being installed as the correct entry type?
1 answer
1 accepted
We ended up having our CA reissue our certificate using a CSR generated from IIS, and then exporting the new certificate as a pfx file with the private key from Windows Cert Manager, and finally, using the importkeystore keytool command to import the certificate into the existing keystore. We updated the config file, restarted BitBucket, and the site is now secure with the new certificate.
I don't know what was wrong with the original keystore that was used. But this alternative method of creating and managing the certificate is viable and easier.
How did you import the .pfx file? Just import into the Windows Cert manager and re-export without the private key? I like this idea, just not quite able to make this path work for me.
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.

Was this helpful?
Thanks!
- FAQ
- Community Guidelines
- About
- Privacy policy
- Notice at Collection
- Terms of use
- © 2024 Atlassian





You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.